The moment an offence, cyber/digital in nature, or involving cyber/digital aspects/evidences, or having cyber/ digital consequences, comes into the picture; the officer coming into the knowledge shall immediately take all necessary steps to protect and safeguard the cyber/digital evidences keeping in view of their critical and volatile electro-magnetic nature. For the purpose, he shall follow the guidelines provided herein. He shall also report the matter forthwith to the IPF, RPF/Post and the Sr.DSC having jurisdiction, with full details available.
On receipt of the information, the IPF, RPF/Post, shall nominate a competent inquiry officer and dispatch him to the place of occurrence (PO) by first available means. The Sr. DSC concerned, satisfying himself of requirement of cyber investigation into the offense, shall report the same to the nearest Cyber Cell, duly nominating the In-charge/cyber cell shall proceed as follows.
- Pre-investigation assessment- The In-charge/Cyber cell (A.E.O) shall collect all necessary information (like- profiles of the suspects, location, circumstances, computer systems involved) and analyze scope of the offense and its possible outcomes.Accordingly, in consultation with the site officer and the E.O, he shall chalk out an enquiry plan. He shall proceed to the PO along with all necessary tools & equipment.
- Evaluation of the Scene of Crime- The digital evidences are very volatile in nature. Those could be available in a number of devices, locations and formats. For example, apart from the standard computer/storage devices, hubs routers, dongles, copiers and fax machines can also have vital information relevant to the case. Therefore, the crime scene should be carefully evaluated before the collection of evedences. While evaluating, the A.E.O should keep taking some brief observation notes (could also be required by the FSLs, later on), draw a network architecture sketch of the scene of crime on ‘as is where is’ and arrange for photography & videography through a trained professional; and document them in the panchanama proceedings.
The crime scenes could be broadly categorized as- (a) House of an individual/s having one or more computer/networks, (b) office or shop of an individual/company like-an IRCTC agent having large no of computer systems spread over several places and connected through several networks, and (c) A public place like- a cyber café or a public information portal manned & maintained by the Govt. organizations directly or through lease holders. The pre- investigation assessments should be modified on the basis of evaluation of the crime scene.
Following evidences should be looked for, noted and photographed. Number of computer systems present, no of them having LAN or internet connections, Types of connections (WiFi- Ethernet), Computer peripherals used, personal appliances (like- hearing aids or spectacles etc.), Network topology and client-server architecture, CCTV/Web camera clippings if any, user management software installed if any, log register maintained if any etc.
- Collection of Physical evidences- Based on the information gathered and inspection of the scene of crime, the A.E.O shall identify and collect all the potential evidences. The physical evidences may include manuals/user guides or receipts of the cyber appliances, left behind diaries, notes/passwords on slips, e-mail IDs, contact numbers or bank account numbers etc.
It is also important to note & sketch the position of the various equipment at the scene of crime. For example, a mouse at the left hand side of the keyboard may indicate the user being dexterous, the number of the reading glass kept beside may reveal exact identity of the user.
- Precautions to be taken while collecting Digital Evidences- Collection of digital evidence require special precautions because, (a) Even the slightest mishandling may vanish or corrupt the evidences, (b) They may not be admissible in the court of law if proper documentation is not done, (c) leveling and preserving digital evidences may require special skills.
- If the systems are ‘off’, those should not be turned ‘on’. If the systems are ‘on’ those should be left’on’ and photographed. The time zone/ system time displayed should be photographed. Perishable evidences should be identified and preserved.
- The E.O should make note of the attached network cables, power lines, all the network connections, modems, telephone lines; and mark them at the both ends- at the equipment connection end and at the source end in the wall.
- The search team shall physically inspect all the storage mediums, take photographs and record observations. Good data encryption should be used and housed in multiple copies at different locations and guarded against mechanical & electronic hazards.
- The E.O shall establish a baseline of contents for authentication and proof of integrity by calculating hash value for each of the contents.
- The E.O shall ensure that some technical person from the suspect side, along with two independent local witnesses, should remain present, identify the equipment correctly, guide and sign the search & seizure proceedings.
- He shall ensure that the provisions of sec. 165 Cr.PC and Sec. 80IT Act are strictly followed.
- A serial number should be allotted to each device. The same should be noted in the panchanama as well as in the ‘chain of custody’ [form-2 of schedule-I).
- Digital Evidence form (DEC)- A proper documentation of the processes used (like- kind of software, version, time and media on which the evidence I being copied etc.) should be done for every device separately.
- The E.O shall image the evidences forensically, acquire hash value and record the process, the tool, time and hashing algorithm in the DEC form (form-3 of Schedule-I) as well as in the Panchanama. The report generated by the forensic tool shall form an enclosure to the DEC.
- The Hard Disk or any other internal parts, once removed from the system, should be photographed along be with the system. The serial no., case no. and sections of law involved should also bee marked to the extent possible.
- Chain of custody should be prepared. As electronic evidences are prone to tamper/damage, it is necessary to know by whom, when, where, what and why the evidence was transferred. Therefore, once the evidence is collected and every time that is transferred, that shall be properly documented and no one other than the ‘persons entrusted’ should have access to that.
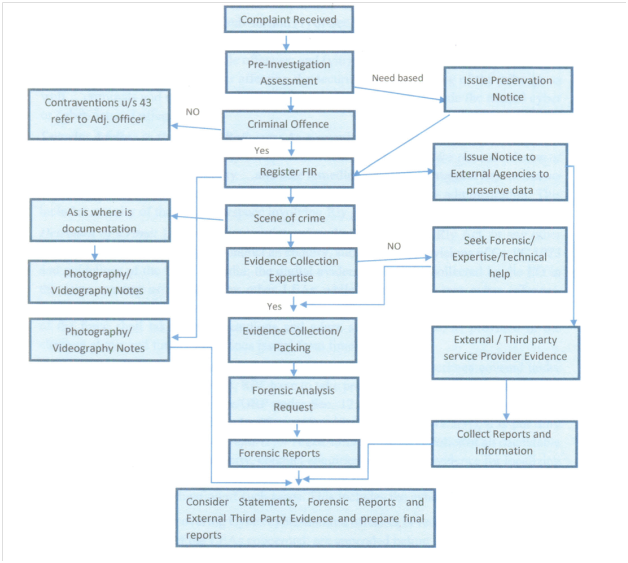
Flow chart/Cyber investigation
How to do collection of Digital evidences (Switched off/on Systems and Cell phone systems) Read More: