A ZLoader malware campaign is exploiting a nine-year-old flaw in Microsoft’s digital signature verification to steal credentials and sensitive information using remote monitoring tools.
According to Check Point Research, which has been tracking the sophisticated infection chain since November 2021, it has been attributed to a cybercriminal group dubbed MalSmoke, citing similarities with previous attacks. “The infection chain incorporates legitimate remote management software (RMM) to gain access to the target machine.” After injecting its payload into a signed DLL, the malware further evades the system’s defenses by exploiting Microsoft’s digital signature verification.
As a banking trojan at its core, ZLoader has been used by many attackers to steal cookies, passwords, and other private information from victims’ machines, but it has also gained notoriety for acting as a distribution platform for Conti ransomware, according to a U.S. State Department advisory. The Cybersecurity and Infrastructure Security Agency (CISA) will be created in September 2021.
As of January 2, 2022, the campaign claimed 2,170 victims in 111 countries, with the majority of victims in the United States, Canada, India, Indonesia, and Australia. It also eludes detection and analysis by obfuscating itself and using other detection-evasion methods.
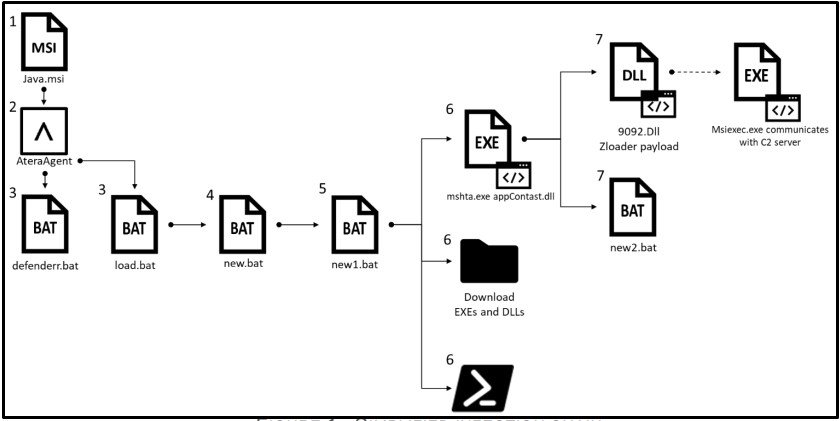
Users are tricked into installing a legitimate enterprise remote monitoring software called Atera, which is then used to upload and download arbitrary files and execute malicious scripts. However, the exact method of distributing the installer file is still unknown.
Two of the files are used to exclude Windows Defender from the attack, and a third is used to retrieve and execute next-stage payloads, including a DLL called “appContast.dll” that is used to run the ZLoader binary (“9092.dll”).
It’s noteworthy that appContast.dll is not only signed by Microsoft, it has also been injected with a malicious script to load the final-stage malware. Originally an app resolver module (“AppResolver.dll”), the file has been tweaked and injected with a malicious script to load the final-stage malware.
A vulnerability tracked as CVE-2013-3900 — a WinVerifyTrust signature validation flaw — allows remote attackers to execute arbitrary code via specially crafted portable executables by making subtle enough changes to the file without invalidating the digital signature.
Although Microsoft corrected the bug in 2013, it revised its plans in July 2014 to no longer “enforce the stricter verification behavior as a default functionality on supported releases of Microsoft Windows” and made it available as an opt-in feature. The malware author can modify a signed file when this fix is disabled by default, Cohen explained.
According to Check Point malware researcher, Kobi Eisenkraft, the ZLoader campaign authors are still working on defense evasion methods every week and advise users to refrain from installing software from unknown sources and verify executable files with Microsoft’s Windows Authenticode signature verification.
You may also like
-
Dhaka Police arrests Turkish ATM hacker six months after escaping from Agartala
-
What is phishing?
-
Remote hacking is possible for Garrett walk-through metal detectors.
-
Code Signing Certificates are being used by new BLISTER malware to avoid detection.
-
Bug in macOS, Gatekeeper’s security can be bypassed by malware.