As COVID19 spreads rapidly worldwide, there has been a big increase in the malicious activities. Recently, a group of hackers tried to breach the World Health Organization (WHO), according to a report by Reuters. WHO Chief Information Security Officer Flavio Aggio said the identity of the hackers was unclear and the effort was unsuccessful. The hack was discovered by Alexander Urbelis, a cyber-security expert and lawyer who looks for suspicious internet activity. He said he discovered the activity on March 13, when hackers introduced a fake, malicious site that pretended to be the WHO’s email system. “Criminals are disguising themselves as WHO to steal money or sensitive information,” the WHO said in a press release.” Many other organizations have also been targeted by the hackers during the coronavirus pandemic.
According to the Subex, India faced the most cyber-attacks in the world. The most commonly targeted sectors in India were critical infrastructure followed by banking, defense and manufacturing. The report says the attacks were carried out through ‘botnets’ that are used to inject malware into a victim’s device, allowing those controlling the botnet to take control of the device, gather information of the device and even remotely make the victim’s device perform specific tasks such as sending information back to the person controlling the botnet.
A ‘botnet’ is a set of devices, which have computing ability and can be connected to each other through the internet — for example, computers, drones, and smartphones can be connected to each other via the internet.
Recent study shows ‘Phishing’ emails have spiked by over 600% since the end of February as cyber-criminals look to capitalize on the fear and uncertainty generated by the COVID-19 pandemic, according to Barracuda Networks.
The security vendor observed just 137 incidents in January, rising to 1188 in February and 9116 so far in March. Around 2% of the 468,000 global email attacks detected by the firm were classified as COVID-19-themed. As is usually the case, the attacks used widespread awareness of the subject to trick users into handing over their log-ins and financial information, and/or unwittingly downloading malware to their computers
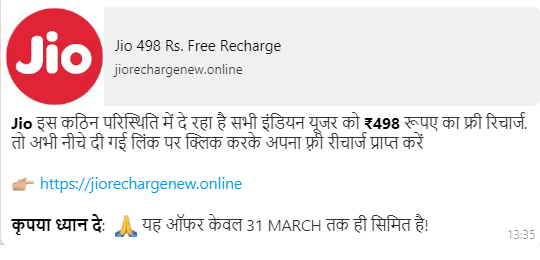
As well as the usual lures to click through for more information on the pandemic, some scammers are claiming to sell cures and/or face-masks, while others try to elicit investment in companies producing vaccines, or donations to fight the virus and provide support to victims.
In many phishing emails there are bound to be some discrepancies. In one instance, an email sent in the name of WHO was asking individuals to make donations in crypto currencies such as Bit coins. In reality WHO doesn’t take donations in Bitcoin. Similarly, an email spotted by Check Point was signed off by a doctor from WHO based in Italy. However, the cyber security firm’s researchers could not find a doctor by the name of Penelope Marchetti with WHO during their online searches.
Any email coming from an unknown sender with very little information in the body text and a request to click on a link or attachment should not be entertained at all, unless one has verified the sender’s identity first. Clicking on link can land one a malicious webpage while a malicious attachment can install nefarious malwares like Emotet on the system and open doors for multiple other malwares. User can lose control over their system and the critical personal or financial data on it may end up on Dark Web for sale.
Unfortunately, computer users are as exposed as ever to phishing scams like these, according to new research. Several security awareness training company claimed that 38% of untrained end users are susceptible to phishing, i.e. they will fail realistic phishing scenarios
Now the question is how to protect yourself?
While phishing emails leveraging coronavirus are new, the same precautions for email security still apply.
1) Be ware of any emails attempting to get users to open attachments or click links. Anti-malware and anti-phishing solutions can be especially helpful to prevent malicious emails and payloads from reaching intended recipients, but even with such protections in place, caution should always be used since no solution catches everything.
2) Watch out for any communications claiming to be from sources that you normally would not receive emails from. These are likely phishing attempts. While receiving COVID19 related emails from legitimate distribution lists to which you belong is becoming common, emails from organizations that you do not regularly receive messages from should be scrutinized closely.
3) Use caution with emails from organizations you regularly communicate with. Brand impersonation is quite prevalent in COVID19 related email attacks, so use caution opening emails from organizations you expect to hear from. This especially applies to those in the healthcare industry since it is being targeted by cyber-attacks trying to capitalize on the pressure resulting from handling an influx of COVID19 cases.
4) Find credible charities and donate directly. A common tactic for coronavirus-related scams is asking for donations to help those affected by the pandemic. To avoid falling victim to one of these attacks, don’t respond to email requests for donations. Instead, find credible charities helping with coronavirus efforts and donate directly through them. It’s also highly unlikely that any legitimate charities are taking donations through Bit coin wallets, so seeing that in an email should be a red flag.
References:
https://www.infosecurity-magazine.com/news/covid19-drive-phishing-emails-667/
https://www.techrepublic.com/article/667-spike-in-email-phishing-attacks-due-to-coronavirus-fears/
You may also like
-
Dhaka Police arrests Turkish ATM hacker six months after escaping from Agartala
-
What is phishing?
-
Zloader Banking a new Malware attack can be bypass Microsoft Signature Verification.
-
Remote hacking is possible for Garrett walk-through metal detectors.
-
Code Signing Certificates are being used by new BLISTER malware to avoid detection.