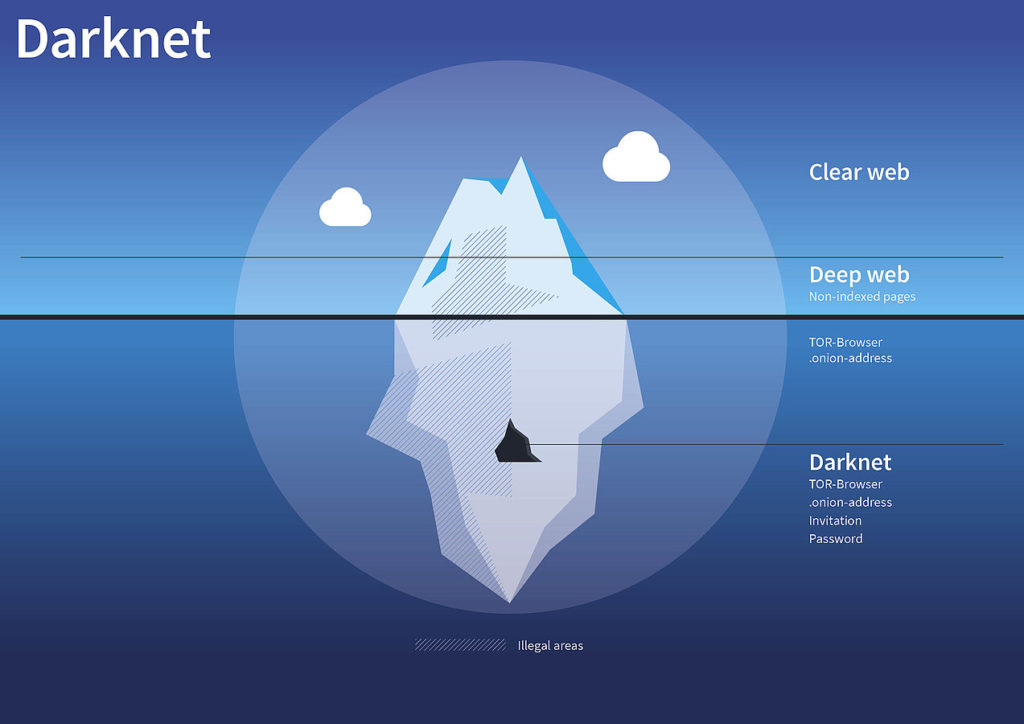
- Darknets- In the realm of Dark web, it is the category of networks available only to a select group of people through specific authorization, configuration or software; but are not available to the general internet users. These are not visible in the search engines like- Google or Yahoo. Due to anonymity, these are the safe havens of the international arms/drug mafia, money launderers and militants. Breaching the darknets are the growing challenges before the LEAs across the world.
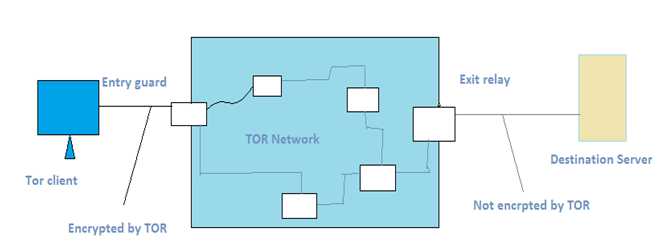
- TOR (The Onion Router)- is the most widely used open source software enabling anonymous communication. It uses onlin routing protocol i.e. transmitting the user’s web traffic through a series of computers(nodes) located around the globe, which makes a user’s location /internet activities difficult to track. It deploys virtual ‘entry guards’ to secure entry into the darknet, directs the traffic through a free worldwide volunteer overlay networks, and then hands them over to the visible networks through virtual ‘exit relays’. A typical architecture is illustrated below-
- IIP or I2P (Invisible internet Project)- Created in 2003, it is an open source network layer that allows for censorship- resistant peer-to-peer communication. The anonymity is achieved by end-to-end encryption and routing that through a volunteer run huge network of computers (I2P nodes) distributed around the world.
Zeronet- Created by Tamas Kocsis in 2015, it is the most recent and more secure than TOR. It is a decentralized web – like network of peer-to-peer users. Here, instead of having an IP address, the sites are identified by a public key (bitcoin address). It is not anonymous by default, but supports routing traffic through TOR network.
You may also like
-
Importance of user ID’s in social media investigations
-
Cyber Crime: Definition, Types and Prevention
-
Section 84C : Punishment for attempt to commit offences (Inserted Vide ITA-2008)
-
Section 84B: Punishment for abetment of offences (Inserted Vide ITA-2008)
-
Section 80 : Power of Police officer and other Officers to enter, search, etc